Canon Pixma Photo Printer Hacked to Run Doom
![]()
The “Internet of Things” is likely what the future holds, but it’s a future that has it share of security concerns. As more and more devices are making their way online, hackers will have newer points of entry into our lives.
Case in point: a security researcher has shown that Canon Pixma printers can be hacked to run custom code. As an example, he loaded the game Doom onto the printer.

In an article published at Context, researcher Michael Jordan writes that the vulnerability lies in the web interface that Pixma printers offer to provide information to owners. It’s a browser-based panel that lets users check ink levels, print test pages, and check for firmware updates.
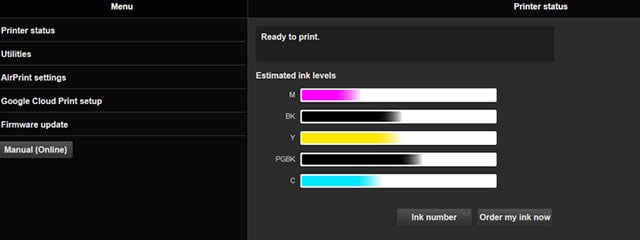
The interface doesn’t require user authentication, but at the same time it’s relatively benign… or so Canon thought.
Jordan found that the firmware update process can be used to hack the printer. By changing the settings for where the printer should look for its next firmware update, Jordan was able to load custom software onto the printer.
![]()
This technique could be used by hackers to install software that spies on the photos and documents being printed, or worse, to allow hackers an entry point into your home network.
Here’s a video that shows Doom running on a Pixma printer (he had issues getting the game’s colors correct, but it’s definitely running):
After contacting Canon about this issue, Jordan was told that future versions of Pixma printers will come with username and password requirements for the web interface.
P.S. Last year security researchers showed how the Wi-Fi on wirelessly connected DSLRs can be used to spy on owners.
Image credits: Photographs and screenshots by Michael Jordan/Context