
Facebook is Testing a Photo Protection Feature
Facebook is rolling out new tools to its users in India that will protect profile photos and help combat image theft.

Facebook is rolling out new tools to its users in India that will protect profile photos and help combat image theft.
Check out this Nikon DSLR rig, which apparently uses a pistol-style grip for triggering the shutter. It seems this kit looks too much like a firearm for the TSA's liking.

The United States has issued a new ban on cameras, laptops, tablets, and other portable electronic devices as carry-on items for flights from 10 airports in 8 countries. The new rules take effect Tuesday.

Removing a lens from modern cameras is usually extremely easy. It's a great feature for photographers who switch lenses a lot, but it can also make it quick and easy for thieves to steal a pricey lens. Now there's a new open source accessory called Mark's Lens Safe that helps protect against this type of common theft.

Yahoo announced back in September 2016 that an estimated 500 million accounts were stolen in late 2014. If you haven't changed your Yahoo or Flickr account passwords yet, there's now some even worse news: Yahoo just revealed that 1 billion accounts were hacked in late 2013.
As a photographer, you obviously want to spend your time focusing on your passion: capturing great images, being creative, and making art. Unfortunately, in our connected world, photo security is a very real concern. This article is a comprehensive guide on protecting your photos from online image theft.

Drone defense vary greatly—we've seen everything from drone-specific shotgun shells to trained police eagles. But none of those have anything on DroneShield's new DroneGun, a massive drone jamming system that would look totally at home on the set of Star Trek.

Strapping thousands of dollars of camera gear to your body and navigating large crowds of intoxicated fans can present unique risks to professional music photographers. Never is that risk greater than at music festivals.

There are a bunch of ways to make money through Instagram: you can sell prints, attract potential clients, you can even set up an account for your pooch. But one 10-year-old in Finnish kid squeezed $10K out of Instagram without having to post a single photo... he hacked the platform instead.

Earlier this month, Instagram finally added support for switching between multiple accounts in the same app. Now the photo sharing service is adding another oft-requested feature: 2-factor authentication.
That's the security feature that texts a security code to your phone when you're logging into your account to verify that it's actually you doing the login. It makes the login process slightly more cumbersome, but what you get is a lot more protection from people trying to hack in.

Check out this crazy-looking rifle. No, it's not from a sci-fi movie -- it's actually an anti-drone counter-weapon called the DroneDefender that's designed to bring down drones using disruptive radio waves.

On September 23rd, Pope Francis will be visiting Washington D.C. and rolling through the streets during a Papal Parade in his Popemobile. The Secret Service is working hard on security preparations leading up to the visit, and yesterday it published security policies for law enforcement to enforce.
Among the banned items at the parade are firearms, explosives, drones, and selfies sticks.

Camera drones have opened a whole new world of possibilities for photographers looking for a way to capture aerial images, but the meteoric rise in drone adoption has also opened up Pandora's box as well. Now a new industry is emerging alongside the booming drone industry: anti-drone defense systems.

Last week we reported that CVS's photo printing website had been taken offline in response to a possible breach of credit card data at its third party vendor. It turns out that same vendor powers many other huge photo printing service sites out there, and those sites are now down as well.

I just installed an ANKR in my camera bag. Over the past 10 years I’ve had this reoccurring dream about my camera gear and my backpack being stolen. I’ve actually had two cameras stolen over the years, unfortunately.

Selfie sticks may be growing in popularity, but bans of the photo accessory have been increasingly common as well. First sports stadiums started prohibiting spectators from using the sticks, and then major museums started following suit. Next in line: major theme parks.
Disney World and Disneyland are both issuing complete bans on selfie sticks, meaning guests won't be able to bring them into any of Disney's US-based theme parks. Bans will also be implemented at Disney's parks in Paris and Hong Kong.

The 2015 French Open is underway in the tennis world, and one of the big news stories of the first round doesn't even have to do with tennis. After tennis superstar Roger Federer easily won his first round match today, a young fan sprinted onto the tennis court and attempted to take a selfie with Federer.

An Indian security researcher has been awarded $12,500 by Facebook after discovering a ridiculously simple hack that could have wiped out vast numbers of photos on Facebook.

Yesterday we reported that a DJI Phantom quadcopter operator had accidentally crashed his camera drone onto the lawn of the White House at 3 in the morning, causing a security panic among those tasked with ensuring the President's safety (later reports suggest the man was drunk).
DJI wants to make sure this type of incident never happens again: the company is issuing a mandatory firmware update that will disable its camera drones in Washington DC's no fly zone.

Photographers have long been grumbling about the FAA's tight regulations for camera drone usage, and the actions of one operator over in Washington DC aren't going to help the cause. An anonymous DJI Phantom owner and government employee crashed his DJI Phantom quadcopter on the White House lawn yesterday morning, causing a lock down of the President's residence.

As the quality of cameras becomes better and better, there's a new security issue emerging that you may have not thought about: fingerprints being stolen from photos.
Hackers are reporting that a person's fingerprints can be reproduced using public photos that show their hand.

Want a camera that can automatically encrypt photos after taking them? A hacker named Doug did. After having this idea for years without seeing camera companies offer it, he decided to take matters into his own hands and make it happen himself.
What resulted is a new custom firmware for the Samsung NX300 that adds photo encryption to the camera.

We've published a number of posts in the past on how you can recover photos that were accidentally deleted from your computer or memory card. But what about when you delete a photo and expect it to actually be gone forever?
The ease with which deleted files can often be recovered means that you should be careful when selling or tossing hard drives or memory cards -- your photos and files might end up falling into the wrong hands if someone decides to try data recovery.

While the video above is a bit short and doesn't explain what exactly is going on, the technology at work in the video is intriguing to say the least -- especially for CCTV cameras.

If you use Dropbox to store and share your photos, the recent news of an alleged username and password hack probably has you worried. But according to Dropbox, it shouldn't. Not only was Dropbox not hacked, but any usernames/passwords that might have been compromised were reset months ago due to suspicious activity.
The "Internet of Things" is likely what the future holds, but it's a future that has it share of security concerns. As more and more devices are making their way online, hackers will have newer points of entry into our lives.
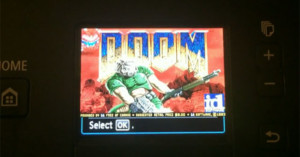
Case in point: a security researcher has shown that Canon Pixma printers can be hacked to run custom code. As an example, he loaded the game Doom onto the printer.

Yesterday, the TSA announced that those flying to the US from certain parts of the world may be asked to power on their electronics to make sure they are not hiding explosives as part of new security measures. If the gadget doesn't turn on, you'll have to leave it behind and could be subject to additional screening.

Many photographers love photo-themed T-Shirts -- from camera brand-specific ones, to the cool offerings of Dodge & Burn, all the way to funny and maybe inappropriate shirts like the Camera Sutra. But, as Fro Knows Photo photographer Jared Polin learned recently, you might wanna leave the photo-themed T-Shirt at home when you visit your local amusement park.
If you regularly share snapshots of your life online, turning off geotagging isn't a very reliable way to keep your location private. Everything seen in the photo -- including faint reflections -- can be used to figure out where you were with scary accuracy.

If you care about endangered animals that are hunted for their parts, here's something important you should keep in mind: make sure you scrub the GPS data on the images prior to sharing them online. Poachers have reportedly been turning to geotagged photos on social networks in order to find out where they can make their next kill.

Japanese security firm Security System Co. (gotta give them credit for originality) recently got in touch with the incredibly talented designer Chicara Nagata -- who creates high-end custom-made motorcycles -- to see if he would build them a security camera... they left the details up to him.
So, naturally, he chose to do what he does best and built a motorcycle ... or a security camera ... or whatever you want to call this strange and strangely awesome hybrid.

A 16-year-old New Jersey kid is making headlines today after embarrassing the Port Authority, NYPD and private security this weekend for the sake of some rooftopping pictures that ultimately led to his arrest.

It's in the Oxford Dictionaries Online, it's even been dubbed the word of the year 2013, and now, it's also a highly secure way to encrypt your personal data. We're talking, of course, about the selfie, which added the last of those three abilities to its repertoire recently with the debut of iOS app FaceCrypt.

A popular iOS and Android app that promised to generate torrents of Instagram likes and followers for its users also swiped thousands of passwords for the service, and is now being called a massive scam.

A Malaysian researcher may have dealt a major blow to image thieves by using the mathematical formulas behind Sudoku puzzles to create hidden, super-strong watermarks.

The western world was sent into a brief paranoid frenzy when whistleblower Edward Snowden leaked government information about the surveillance of the National Security Agency (NSA). I say brief, because it seems to have been forgotten by a large number of people; it seemed like it was just more news. The revelations, and more that followed, showed how the NSA record phone calls and data and more controversially; that they use information from emails and social networking sites.

What do a loaded gun, a stun gun disguised as a pack of cigarettes and an inert grenade all have in common? Pictures of all of them are to be found on the Transportation Security Administration's (TSA) new Instagram account, where the government agency is doing its best to show the public the kinds of dangerous things its employees are confiscating on a daily basis.
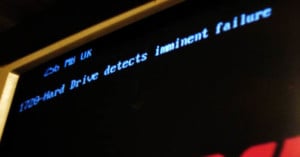
I had a hard drive fail on me once. It was a total nightmare. I lost two years of digital photos and all of my music that i’d digitized. Never again.
Thankfully this happened to me before I was a professional photographer and it was just my own images. Not a wedding client's. If you charge people for your photography, you need to be professional and have a proper bomb-proof backup strategy.

If you're planning to attend the Kentucky Derby early next month, you might want to make sure you'll be content with capturing your memories with a smartphone or point-and-shoot. Churchill Downs, the racetrack that hosts the famous horse race, has unveiled new security measures that will prevent attendees from bringing certain items onto the grounds. Among them: all interchangeable lens cameras.

Having your camera stolen is not a fun experience. If you're not fortunate enough to have a camera that catches its own theft in progress, your recovery options are limited to services like Stolen Camera Finder, CameraTrace and, the most likely fix, a good insurance policy.