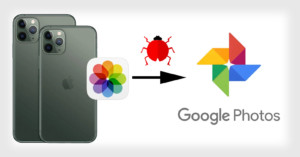
Google to Fix ‘Bug’ That Gives iPhones Unlimited Full-Size Photos Storage
Well, it was fun while it lasted. We reported over the weekend that iPhone users have been enjoying free and unlimited original-quality photo backups through Google Photos thanks to the ultra-efficient HEIC file format. Google is now calling it a "bug" and saying that it will be fixed.